EDR Endpoint Detection and Response
Deliver continuous, comprehensive endpoint visibility that spans detection, response and forensics to ensure nothing is missed and potential breaches are stopped.
What is EDR?
Endpoint detection and response (EDR) solutions detect threats across your environment. Investigate the entire lifecycle of the threat, providing insights into what happened, how it got in, where it has been, what it’s doing now, and how to stop it. By containing the threat at the endpoint, EDR solutions help eliminate the threat and prevent it from spreading.
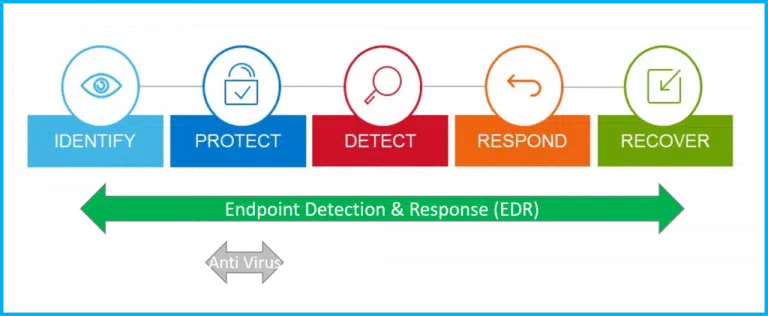
How Does EDR Work?
EDR security solutions record the activities and events taking place on endpoints and all workloads, providing security teams with the visibility they need to uncover incidents that would otherwise remain invisible. An EDR solution needs to provide continuous and comprehensive visibility into what is happening on endpoints in real time.
An EDR tool should offer advanced threat detection, investigation and response capabilities — including incident data search and investigation alert triage, suspicious activity validation, threat hunting, and malicious activity detection and containment.
Intelligent & Efficient Threat Mitigation

Instant remediation
Analysts can quickly uncover details of an attack without crafting complicated queries, then easily pivot directly from investigating to remediating affected devices by executing a full suite of remediation actions from machine isolation and process killing to removing persistence mechanisms - all from within an intuitive interface.

Threat Intelligence
Threat intelligence aggregates multiple threat feeds and cross-examines those feeds against machine learning analysis to rank the various threat feeds based on their historical accuracy for particular types of threats from various adversary groups. This enables our EDR solution to determine the correct threat intelligence source to respond quickly and with precision, which simplifies the investigation and response process.

Detection accuracy and speed
Our EDR solutions identify threats quickly with a high degree of accuracy using behavioural analysis that leverages cross-machine correlations and enriched data from across all endpoints in real-time. Our EDR solutions earned the highest product score in the 2020 Forrester Wave for Enterprise Detection and Response, and the MITRE ATT&CK evaluations highlight the superior proficiency of our EDR solutions in quickly detecting and correlating threats to instantly deliver the complete story of an attack as an easy to interpret, interactive visual representation.

AI / ML-powered detection and correlation
Artificial intelligence and machine learning surface advanced threats by detecting subtle indicators of behaviour. Certain malicious behaviours are only identifiable after analysing enterprise-wide data sets against machine learning. Monitoring via a machine-by-machine basis only can overlook nuanced adversaries whose activity can only be detected when the environment as a whole is analysed and cross-examined against machine learning.
Why choose SR Cloud Solutions?
SR Cloud Solutions has a 25-year track record of supplying managed security services an solutions to many organisations in different industries.
- The best technology – highest levels of accreditation with the world’s leading vendors such as Crowdstrike, Cisco, Fortinet, and Palo Alto.
- Skills and expertise with a UK-based 24/7 Security Operations Centre (SOC).
- We are a Joscar accredited business which means we are certified to work with leading defense companies who require the highest standards of cyber security.
- We are experts in Cloud infrastructures such as Microsoft Azure so we can provide expert security consultancy on hybrid cloud environments and how best to secure and monitor those environments including Cloud Governance.
Book a meeting with one of our consultants to learn more or read on more below to find out more about our EDR Solutions.
EDR Benefits

Endpoint Visibility
Real-time visibility across all your endpoints allows you to view adversary activities, even as they attempt to breach your environment, and stop them immediately.

Behavioral Protection
Relying solely on signature-based methods or indicators of compromise (IOCs) lead to the “silent failure” that allows data breaches to occur. Effective endpoint detection and response requires behavioral approaches that search for indicators of attack (IOAs), so you are alerted of suspicious activities before a compromise can occur.

Fast Response
EDR that enables a fast and accurate response to incidents can stop an attack before it becomes a breach and allow your organization to get back to business quickly.

Threat Database
Effective EDR requires massive amounts of telemetry collected from endpoints and enriched with context so it can be mined for signs of attack with a variety of analytic techniques.

Insight and Intelligence
An endpoint detection and response solution that integrates threat intelligence can provide context, including details on the attributed adversary that is attacking you or other information about the attack.

Cloud-based Solution
Having a cloud-based endpoint detection and response solution is the only way to ensure zero impact on endpoints, while making sure capabilities such as search, analysis and investigation can be done accurately and in real time.
Join Other Leading Companies Who Trust SR Cloud Solutions







Frequently Asked Questions
An endpoint detection and response (EDR) solution detects threats across your environment. It investigates the entire lifecycle of the threat, providing insights into what happened, how it got in, where it has been, what it’s doing now, and how to stop it. By containing the threat at the endpoint, the EDR solution helps eliminate the threat and prevent it from spreading. Your data is only as secure as the endpoint it lives on, which brings us to our next question.
Endpoints can range from the more commonly thought of devices such as:
- Laptops
- Tablets
- Mobile devices
- Smart watches
- Printers
- Servers
- ATM machines
- Medical devices
If a device is connected to a network, it is considered an endpoint. With the growing popularity of BYOD (bring your own device) and IoT (Internet of Things), the number of individual devices connected to an organisation’s network can quickly reach into the tens (and hundreds) of thousands.
EDR focuses primarily on advanced threats that are designed to evade front-line defenses and have successfully entered into the environment. An EPP focuses solely on prevention at the perimeter. It is difficult, if not impossible, for an EPP to block 100 percent of threats. So in the ideal case, an endpoint security solution deploys both EPP and EDR capabilities.
Most EPP (or traditional anti-virus) solutions claim to block the majority of threats. But what about the stealthiest threats that they miss? Having an EDR solution allows you to detect, investigate, and remediate modern threats that are advanced and persistent enough to evade traditional perimeter defenses.
More sophisticated threats that evade perimeter defenses can wreak havoc across your network. Ransomware encrypts sensitive data and holds it hostage from the business until the financial ransom is collected. Meanwhile, malicious cryptomining sits stealthily on the network and exhausts your computing resources. An EDR solution can help you find, contain, and remove the threats fast so you can ensure the security of data on endpoints across your environment.
- Detection
- Containment
- Investigation
- Elimination
Speak to one of our security EXPERTS
Our team is available for a quick call or video meeting. Let's connect and discuss your security challenges, dive into vendor comparison reports, or talk about your upcoming IT-projects. We are here to help.


